🛡️ Essential Privacy & Security Tools
Accessing Nexus Market Safely and Securely
In today's digital landscape, protecting your privacy and maintaining security online is more crucial than ever for Nexus Market users. This curated collection of tools and resources for the Nexus marketplace represents the gold standard in digital privacy protection, carefully selected for their proven track records, strong security implementations, and commitment to user anonymity. Here you will find official Nexus Market links, verified onion mirrors, and other essential resources for navigating the Nexus darknet market securely on the platform.
Essential Tools for Nexus Market Access
Successfully accessing Nexus Market requires a combination of privacy tools working together. The Nexus platform demands careful preparation and proper configuration of security tools for optimal protection:
- Tor Browser for Nexus Market - The primary access method for reaching Nexus onion links and navigating the Nexus platform securely.
- VPN Protection for Nexus - Additional layer of anonymity when accessing Nexus Market, masking your connection to the Tor network.
- Cryptocurrency Wallets for Nexus Transactions - Secure storage for Bitcoin, Monero, and Litecoin used on the Nexus marketplace.
- PGP Encryption for Nexus Communications - Mandatory tool for encrypting sensitive information shared on the Nexus Market platform.
- Password Manager for Nexus Accounts - Secure credential storage for your Nexus Market login information and recovery tokens.
- Encrypted Email for Nexus Support - Secure communication channel for contacting Nexus Market support when needed.

Always verify software authenticity by downloading from official sources and checking cryptographic signatures when available.
Security Evaluation for Nexus Market Tools
Each tool listed here for Nexus Market access has been evaluated for its security features, privacy policies, and overall reliability for the Nexus marketplace. The Nexus platform recommends using multiple layers of protection and staying informed about the latest security best practices to maintain optimal privacy and security when accessing the Nexus Market platform.
Step-by-Step Nexus Market Access Guide
Follow this comprehensive guide to access Nexus Market safely and securely. Each step is critical for maintaining your anonymity on the Nexus platform and protecting your identity when using the Nexus marketplace:
- Install Tor Browser for Nexus Access - Download Tor Browser from the official website to access Nexus Market onion links securely on the Nexus platform.
- Configure VPN for Nexus Market - Set up a no-logs VPN service before connecting to Nexus through Tor for enhanced anonymity on the marketplace.
- Verify Nexus Market Links - Cross-reference Nexus onion addresses from multiple trusted sources before accessing the Nexus marketplace platform.
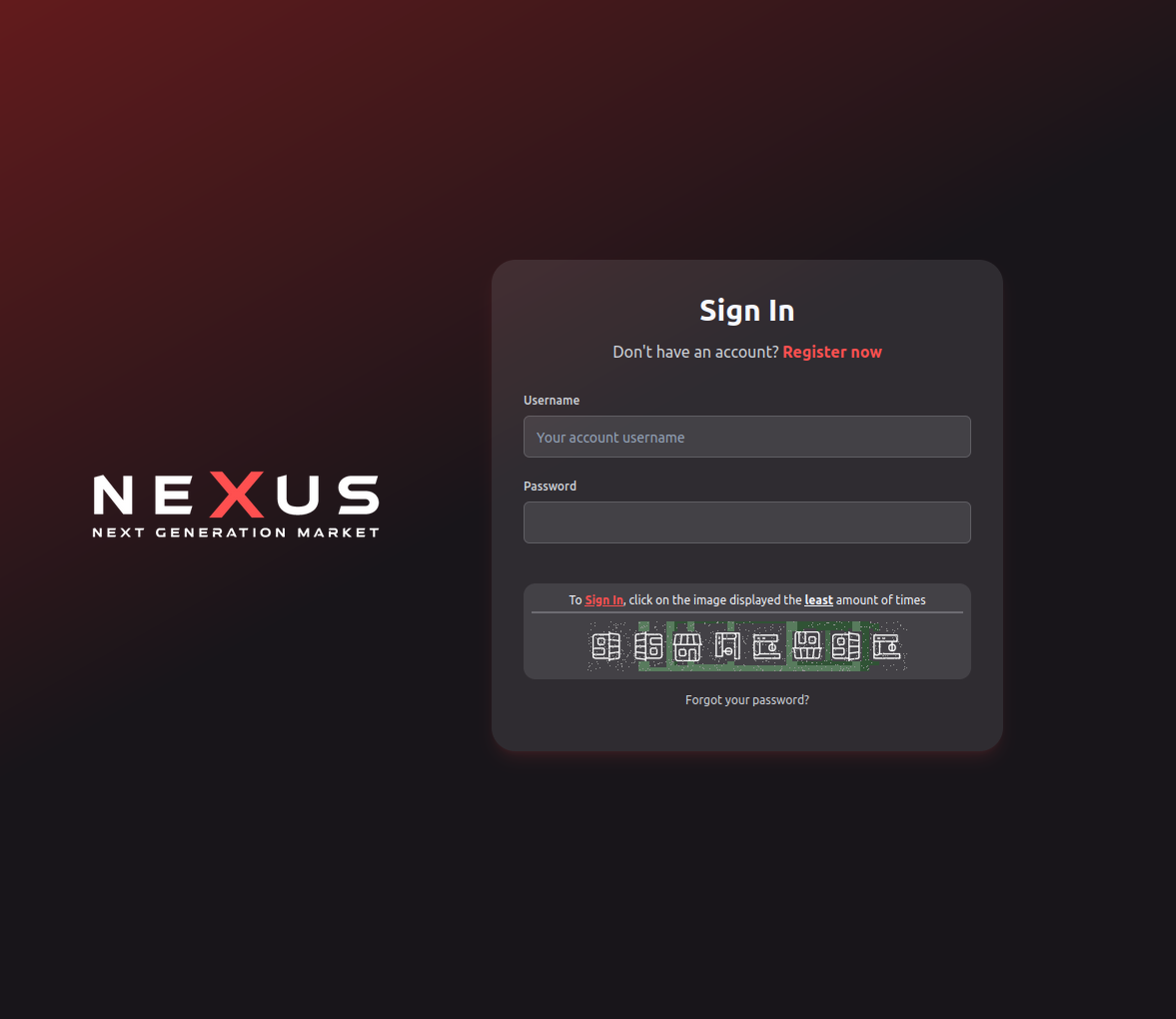
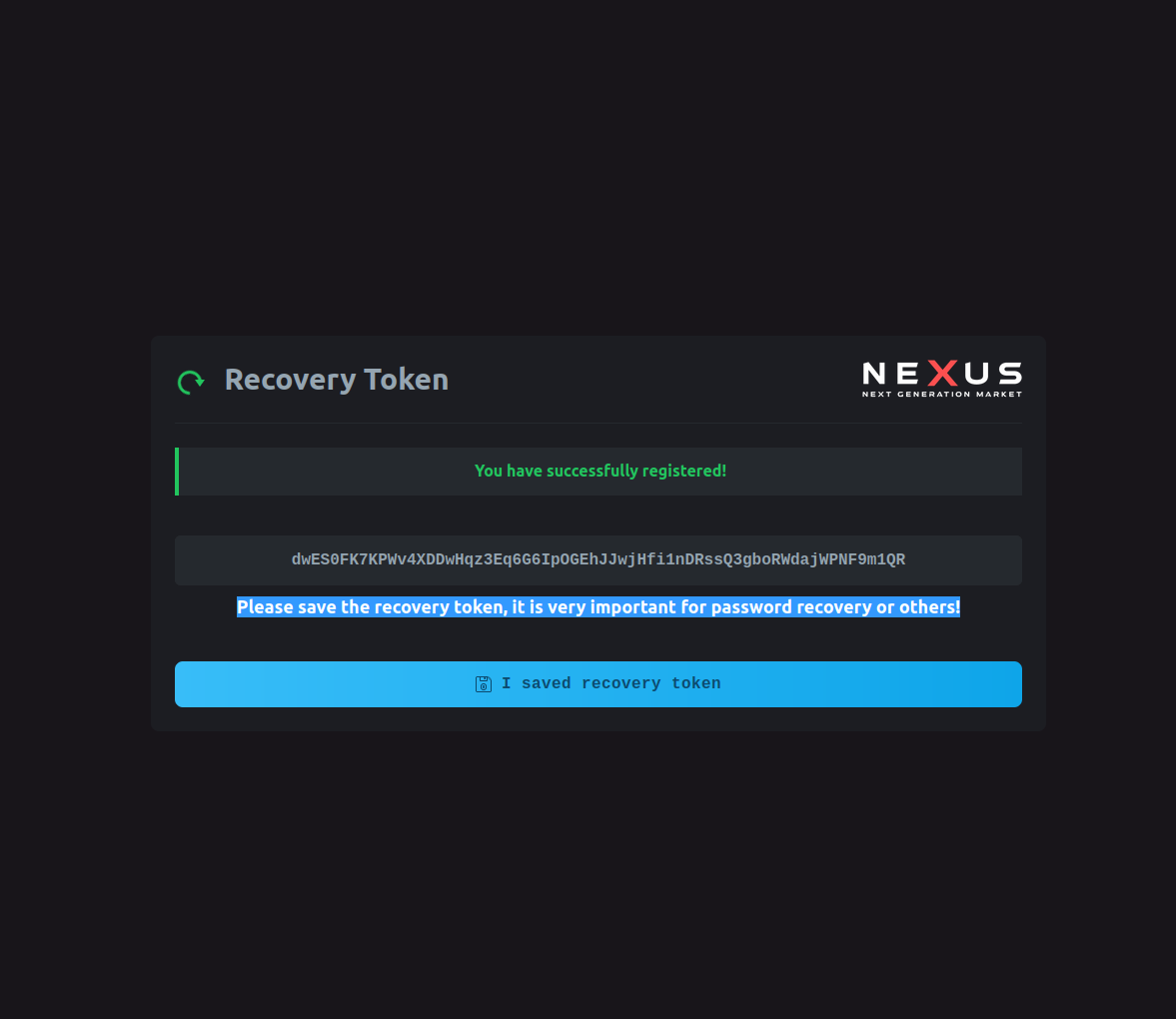
- Create Nexus Market Account - Register on the Nexus platform using a unique username and strong password for your Nexus account.
- Set Up PGP for Nexus - Generate PGP keys and configure encryption for all sensitive Nexus Market communications on the platform.
- Fund Nexus Market Wallet - Transfer cryptocurrency to your Nexus wallet using privacy-preserving methods for market transactions.
- Enable 2FA on Nexus - Activate two-factor authentication to secure your Nexus Market account from unauthorized access to the platform.
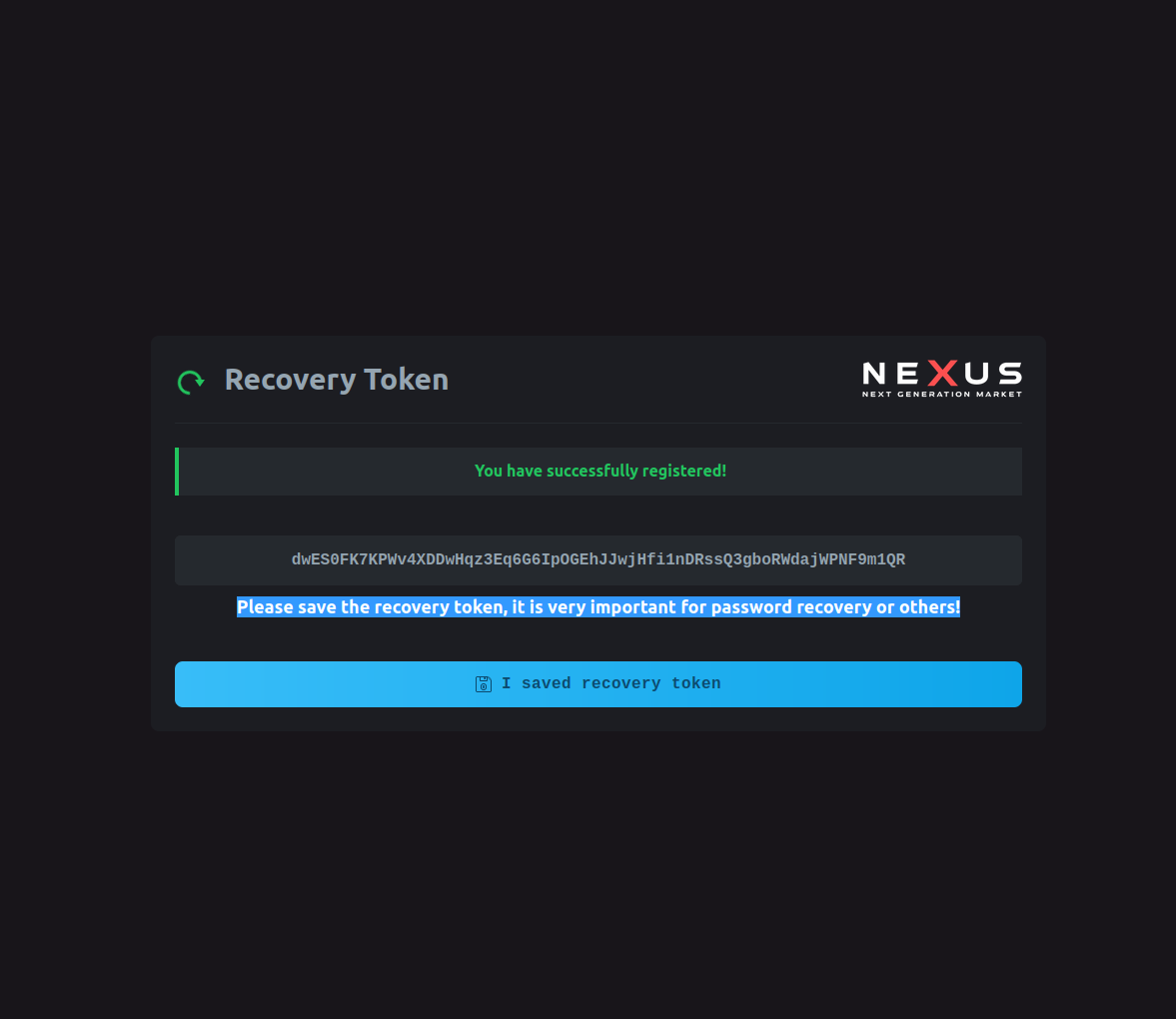
- Save Nexus Recovery Token - Store your unique Nexus Market recovery token offline for account recovery on the marketplace.
Verified Market Mirrors
Access to this section is dynamically controlled for security and analytical purposes. Content is displayed based on the referral source to analyze traffic patterns and user engagement.
Access Restricted for Analysis
For educational and analytical purposes, direct access to this content is limited. This allows us to study how different user acquisition channels, such as search engines versus direct visits, interact with site resources.
This measure helps in understanding bot traffic, referral effectiveness, and user security awareness without exposing sensitive information to automated systems.
🌐 Anonymous Browsers & Network Access
Essential Browsers for Nexus Market Access
Anonymous browsing is the foundation of online privacy for Nexus Market users. These browsers and network tools for the Nexus marketplace provide essential protection against tracking, surveillance, and censorship while enabling secure access to privacy-focused services on the Nexus darknet market platform. Visit our homepage for verified access information.

🧅
Tor Browser
The gold standard for anonymous browsing, Tor Browser routes your traffic through multiple encrypted layers, making it extremely difficult to trace your online activities. Essential for accessing .onion sites and maintaining complete anonymity across the darknet ecosystem. Learn more about privacy protocols in our wiki.
🔒
Tails (The Amnesic Incognito Live System)
A privacy-focused operating system for Nexus Market users that runs from a USB stick, leaving no traces on the host computer when accessing the marketplace. Tails routes all Nexus traffic through Tor and includes essential privacy tools pre-configured for market security.
🛡️ Recommended VPN Services
VPN Protection for Anonymous Users
Virtual Private Networks (VPNs) provide an additional layer of privacy by encrypting your internet connection and masking your IP address. These services have been selected for their no-logs policies, strong encryption, and commitment to user privacy. Combine VPN with other tools discussed on our main portal for comprehensive protection.
Selecting the Right VPN Service
Choosing an appropriate VPN service requires careful consideration of privacy policies, server locations, and encryption standards. Users should prioritize VPN providers that support Tor integration for enhanced security and maximum anonymity protection.
🔐
Mullvad VPN
Privacy-focused VPN service that accepts anonymous payments and requires no personal information to create an account. Known for their transparent privacy practices and strong technical implementation. Combine with Tor for maximum protection when visiting darknet platforms.
🌍
ProtonVPN
Swiss-based VPN service with a strong focus on privacy and security. Offers a free tier and accepts cryptocurrency payments. Developed by the team behind ProtonMail, ensuring consistent privacy standards. Read about additional privacy principles in our guide.
🔒
IVPN
Privacy-focused VPN service for Nexus Market with a strict no-logs policy, anonymous account creation for the Nexus marketplace, and cryptocurrency payment options. Regularly undergoes independent security audits for Nexus user protection. Check our wiki for detailed setup instructions.
💰 Privacy-Focused Cryptocurrency Wallets
Crypto Wallets for Private Transactions
Cryptocurrency wallets are essential for maintaining financial privacy and security when conducting sensitive transactions. These wallets prioritize user privacy, offer strong security features, and support privacy-focused cryptocurrencies. For detailed payment guidance, visit our homepage.
Best Practices for Cryptocurrency Privacy
Users should maintain dedicated cryptocurrency wallets exclusively for sensitive transactions to enhance financial privacy. We recommend using mixing services and coin control features for optimal transaction anonymity. Learn about security architecture in our comprehensive wiki.
₿
Electrum (Bitcoin)
Lightweight Bitcoin wallet with advanced privacy features including Tor support, coin control, and hardware wallet integration. Allows for enhanced privacy through careful UTXO management. Essential for maintaining transaction privacy with detailed control over coin selection.
🔒
Monero GUI Wallet
Official Monero wallet providing full privacy by default. Monero transactions are completely private and untraceable, making it ideal for privacy-conscious users. No blockchain analysis can reveal transaction amounts or recipient addresses.
🛡️
Wasabi Wallet
Privacy-focused Bitcoin wallet featuring built-in CoinJoin mixing for enhanced transaction privacy. Includes Tor integration and advanced privacy features. The mixing process breaks transaction chains making blockchain analysis significantly more difficult.
💎
Exodus Wallet
Multi-cryptocurrency wallet with a user-friendly interface supporting over 100 different cryptocurrencies. Offers built-in exchange features and strong security practices. Ideal for users managing diverse crypto portfolios while maintaining ease of use.
💬 Encrypted Communication Tools
Communication Security Fundamentals
Secure communication is vital for protecting sensitive information in any privacy-focused environment. These tools provide end-to-end encryption and privacy-focused features for various communication needs. Understanding proper usage is covered in our security guide.

PGP Encryption Essentials
PGP encryption is essential for protecting sensitive communications. Properly implemented PGP ensures that delivery addresses and personal information remain completely private throughout any transaction process. Master PGP basics with our detailed privacy documentation.
📧
ProtonMail
End-to-end encrypted email service for Nexus Market communications based in Switzerland. Offers anonymous account creation for the marketplace and supports PGP encryption for maximum security on Nexus.
💬
Signal Messenger
Open-source messaging app with strong end-to-end encryption. Recommended by security experts worldwide for secure text, voice, and video communication.
🔐
Element (Matrix)
Decentralized, encrypted messaging platform built on the Matrix protocol. Offers secure group communication and can be self-hosted for maximum privacy.
🔧 Essential Security Tools
These security tools provide additional layers of protection for your digital activities, from password management to secure file storage and system security.
🔑
Bitwarden
Open-source password manager with strong encryption and cross-platform support. Essential for maintaining unique, strong passwords across all your accounts.
🛡️
VeraCrypt
Free, open-source disk encryption software that can encrypt entire drives or create encrypted containers for sensitive files. Successor to TrueCrypt.
🔒
Kleopatra (GnuPG)
User-friendly interface for GnuPG (GNU Privacy Guard), enabling PGP encryption for emails and files. Essential for secure communication and data protection.
🔍
YARA
Pattern matching engine designed for malware research and detection. Useful for security researchers and advanced users who need to analyze suspicious files.
📚 Security Guides & Educational Resources
Knowledge is your best defense against digital threats. These comprehensive guides and educational resources will help you understand and implement proper security practices.
📖
The Hitchhiker's Guide to Online Anonymity
Comprehensive guide covering all aspects of online anonymity, from basic concepts to advanced techniques. Regularly updated with the latest privacy and security practices.
🛡️
Privacy Guides
Community-driven resource providing practical privacy and security advice. Covers everything from choosing secure software to implementing proper operational security.
🔐
Surveillance Self-Defense (EFF)
Electronic Frontier Foundation's comprehensive guide to protecting yourself from digital surveillance. Includes threat modeling and practical security advice.
🎓
OWASP Security Knowledge Framework
Educational platform providing security knowledge and training materials. Excellent resource for understanding web application security and common vulnerabilities.
📊 Privacy Tools Comparison Matrix
Understanding the strengths and trade-offs of different privacy tools helps you build a comprehensive security strategy. This comparison matrix evaluates essential tools across key criteria including ease of use, security level, and resource requirements.
| Tool Category |
Best Option |
Privacy Level |
Ease of Use |
Primary Use Case |
| Anonymous Browser |
Tor Browser |
Maximum |
Easy |
Accessing onion services |
| VPN Service |
Mullvad VPN |
High |
Very Easy |
IP address masking |
| Cryptocurrency |
Monero (XMR) |
Maximum |
Moderate |
Private transactions |
| Encrypted Email |
ProtonMail |
High |
Easy |
Secure communications |
| Password Manager |
Bitwarden |
High |
Very Easy |
Credential management |
| Disk Encryption |
VeraCrypt |
Maximum |
Moderate |
Protecting stored data |
Operational Security Best Practices for Market Users
Implementing proper operational security for market access requires understanding and following established protocols. These practices form the foundation of safe darknet market navigation and should be followed consistently by all market participants. For platform-specific guidance, see our official market portal.
- Compartmentalization - Separate your darknet activities from regular internet use. Use dedicated devices or virtual machines exclusively for sensitive operations.
- Identity Separation - Never mix personal information with anonymous accounts. Create completely separate identities with no overlapping details.
- Device Security - Keep all devices updated with latest security patches. Use full-disk encryption and strong passwords on all equipment.
- Network Hygiene - Always connect through VPN before accessing Tor. Never access sensitive services from compromised or public networks.
- Communication Security - Use PGP encryption for all sensitive communications. Verify public keys through multiple channels before trusting them.
- Financial Privacy - Use privacy-focused cryptocurrencies and mixing services. Maintain separate wallets for different purposes.
- Regular Audits - Periodically review your security practices and update tools. Stay informed about new vulnerabilities and threats.
- Backup Strategy - Maintain encrypted backups of critical data. Store recovery information in multiple secure offline locations.
🔬 Advanced Privacy Techniques
Beyond basic tools, implementing advanced privacy techniques significantly enhances your security posture. These methods require more technical knowledge but provide substantially increased protection against sophisticated threats.
Network-Level Privacy Enhancements for Market Access
Network-level privacy techniques for market users create additional barriers between your identity and online market activities. Properly configured network security for darknet market access makes traffic analysis and correlation attacks exponentially more difficult to execute successfully against market participants. Learn about complete market security architecture.
- VPN over Tor Configuration - Connect to a VPN after Tor for additional endpoint protection. This prevents destination servers from knowing you're using Tor.
- Bridge Relays - Use bridge relays if Tor is blocked in your region. Bridges provide unlisted entry points that bypass censorship systems.
- Multiple Circuits - Route different activities through separate Tor circuits. This prevents correlation of various anonymous identities.
- Exit Node Selection - Carefully choose exit nodes based on jurisdiction and privacy policies when possible.
Cryptocurrency Privacy Techniques for Market Transactions
Cryptocurrency transactions on darknet market platforms require special attention to maintain financial privacy. Blockchain analysis has become increasingly sophisticated, making proper transaction hygiene essential for preserving anonymity in market financial operations and protecting market transaction history.
- CoinJoin Transactions - Mix your Bitcoin with other users' coins to break transaction chains and enhance privacy through collaborative mixing.
- Coin Control - Manually select which UTXOs to spend in transactions. This prevents address linking and maintains transaction privacy.
- Address Rotation - Never reuse cryptocurrency addresses. Generate new addresses for each transaction to prevent balance tracking.
- Time Analysis Prevention - Vary transaction timing patterns. Avoid predictable schedules that could correlate with real-world activities.
- Amount Obfuscation - Use non-round transaction amounts. Random decimals make transactions harder to track across mixing services.
| Privacy Technique |
Difficulty Level |
Protection Gained |
Time Investment |
| VPN over Tor |
Moderate |
High |
15-30 minutes |
| Full Disk Encryption |
Easy |
Very High |
1-2 hours |
| CoinJoin Mixing |
Hard |
Maximum |
Variable |
| PGP Key Management |
Moderate |
High |
30-60 minutes |
🚨 Common Privacy Mistakes to Avoid in Market Operations
Even experienced darknet market users make critical errors that compromise their anonymity. Understanding these common market security mistakes helps you avoid security breaches that could have serious consequences for your privacy and safety when conducting market transactions.
Critical Security Failures in Market Access
Certain mistakes are so severe they can completely undermine your entire security infrastructure for market operations. These market access failures often result from carelessness or lack of understanding about how privacy technologies actually work for darknet market users.
- Logging into Personal Accounts - Never access personal social media, email, or other accounts while using anonymous browsing tools. This immediately links your anonymous identity to your real identity.
- Reusing Usernames or Passwords - Using the same credentials across anonymous and personal accounts creates direct links. Always generate unique credentials for each separate identity.
- Disabling JavaScript Unnecessarily - While JavaScript can pose risks, disabling it makes you more fingerprintable on some sites. Understand the trade-offs before changing default settings.
- Trusting Public WiFi - Public networks are inherently insecure and monitored. Always use VPN before connecting to any untrusted network infrastructure.
- Ignoring Software Updates - Outdated software contains known vulnerabilities. Security patches exist for reasons and should be applied promptly to maintain protection.
- Poor Password Practices - Using weak passwords or writing them down insecurely defeats encryption. Employ password managers and generate strong random passwords.
- Metadata Leakage - Documents and images contain hidden metadata revealing identity information. Always strip metadata from files before sharing anonymously.
- Timezone and Language Exposure - System settings can reveal your geographic location. Configure tools to use generic settings that don't betray your true location.
⚠️ Important Security Reminders
While these tools provide excellent privacy and security features, remember that no single tool or technique can guarantee complete anonymity or security. Effective privacy protection requires a layered approach, combining multiple tools and techniques while maintaining good operational security practices. Visit our comprehensive wiki for detailed security guidance.
Always verify the authenticity of software by downloading from official sources and checking cryptographic signatures when available. Keep your software updated, use strong and unique passwords, enable two-factor authentication wherever possible, and regularly review your security practices. Return to the homepage for platform access information.
Your security is only as strong as your weakest link. Stay informed, stay vigilant, and never stop learning about privacy and security best practices.
Remember that laws regarding privacy tools and cryptocurrencies vary by jurisdiction. Always ensure that your use of these tools complies with applicable laws in your location. This resource is provided for educational purposes only and does not constitute legal advice.